Web Access Control
Joshua Westgard
October 8, 2015
I. Our Access Control Use Case
- Centralized Authentication System
- Mixed Access Restrictions
- Licenses, Donor Agreements, Fair Use, etc.
- Fedora-level Authorization
II. WebAC Overview
II. WebAC Overview
- Authorization in a Linked Data Context
- Evolving Standard
- ACL is a list of authorizations
- Authorizations are assertions of permission expressed as triples.
III. Rationale
- Fedora 4 Migration Project
- Community of Practice
- Contribute to the Community and Advance Our Own Project
IV. Design
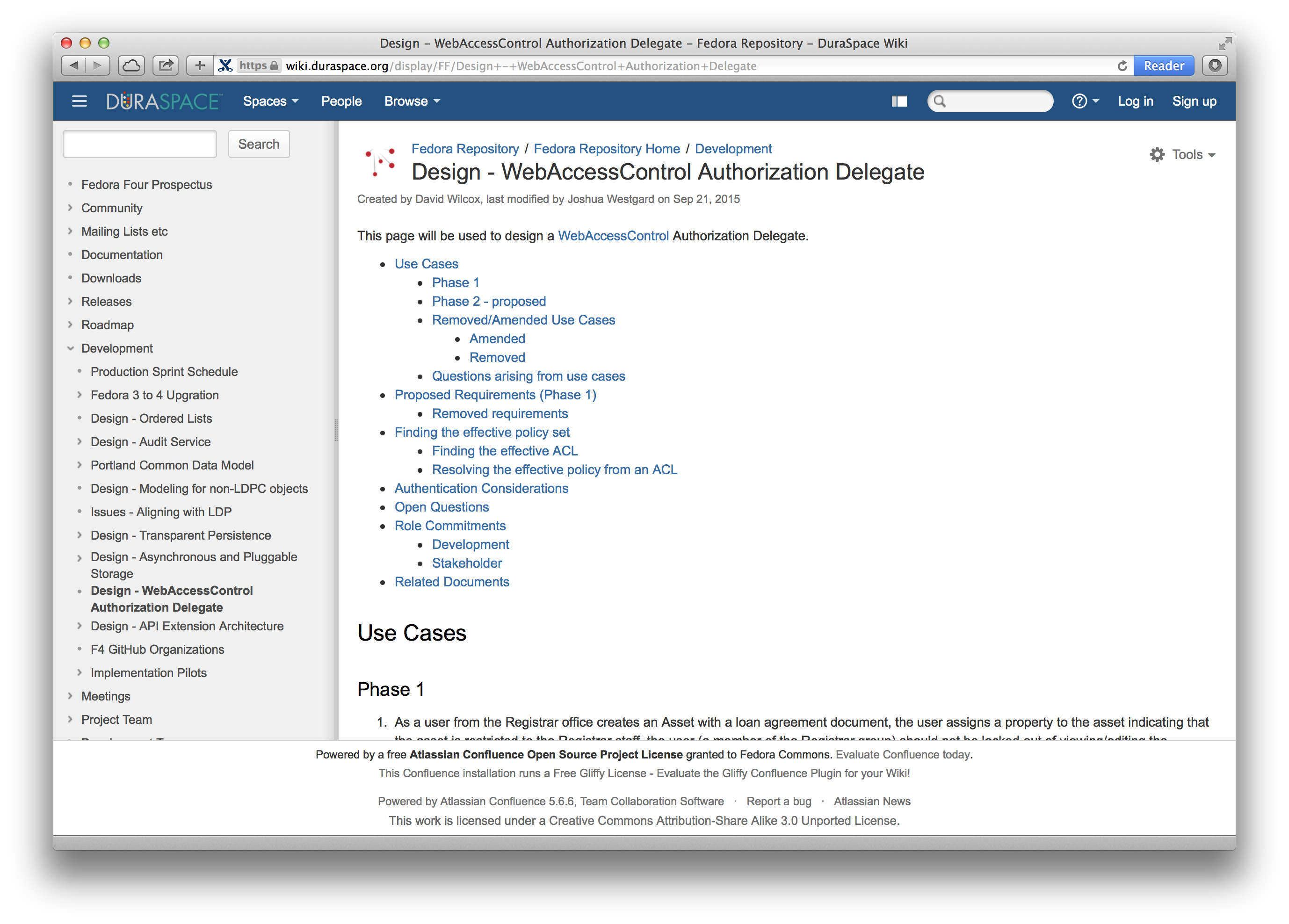
IV. Design
- Lots of Disparate Use Cases
- Asynchronous discussion and Teleconferencing
- Authentication out of scope
- Seven Requirements
- Two Key Algorithms
V. Authorizations as Linked Data
@prefix acl: <http://www.w3.org/ns/auth/acl#>
<> a acl:Authorization ;
acl:accessTo ;
acl:mode acl:Read;
acl:agent </agents/userA> .
VI. Phase 2 and Beyond
- Full Implementation of Classes
- Inheritance?
- Regex Matching?
Thank you!
Joshua Westgard (westgard@umd.edu)
/